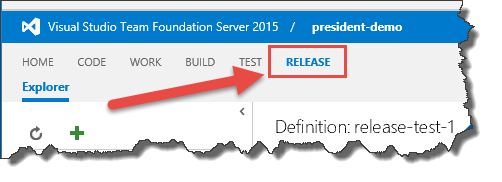
Team Foundation Server (TFS) and Visual Studio Team Services (VSTS) have these really handy features that let you define DevOps release pipelines for your applications. To get to it, go to the web portal for your Team Project and click the Releases tab.
Whether you use Releases (aka. "Release Management") in TFS/VSTS or whether you use some other tool, one of the trickiest parts is handling usernames, passwords, and database connection strings. Each environment that you deploy to probably has different server names and different passwords. Typically, lots of people have the passwords for the development environment but for the production servers, there are probably just a very limited number of people who have that information.
So how do deal with this? How do you make it so that not everyone can see the values?
Use Configuration Variables
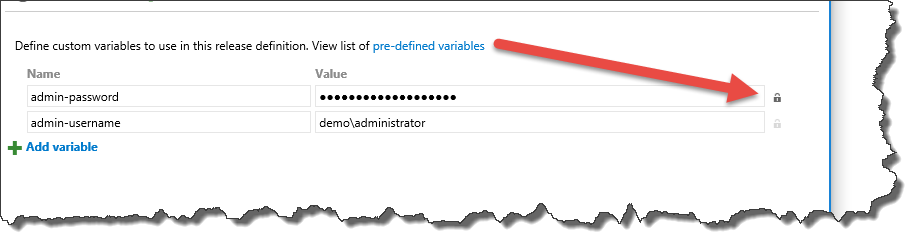
The answer is that you should define configuration variables in your TFS/VSTS release definition. These values can be stored at the Release level or at the Environment level. To specify a configuration variable for the Release, click on the configuration tab and then add the variables. (BTW, we'll handle the encrypted stuff in a moment.)
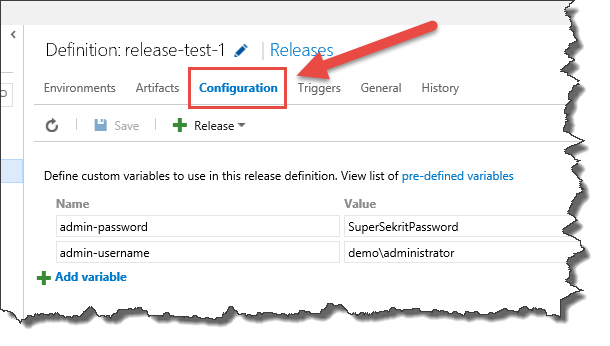
Once you've defined the variables, you can then use these values in the steps (aka. "activities") in your release. You reference them using the $(variable-name) format as shown in the following image.
"But everyone can still see the password!"
Ok. So you've got the values being used as configuration variables. But you still have the problem of the password being visible in cleartext. This is an easy fix but it's a little tough to see. The answer is actually hidden in plain sight. (BTW, thanks to my friend and fellow MVP, Angela Dugan @OakParkGirl for pointing this out.)
Go back to the Configuration tab where you defined the configuration variables for the release.
Hidden to the right of the value is a little lock icon. Click that lock button and save your release definition. Voila! that value is now encrypted.
That's it. You're done.
By the way, this same trick works on TFS Build Variables, too.
-Ben
-- Looking to going good at DevOps & Scrum? Need help getting your TFS/VSTS Releases working? Trying to figure out how to achieve build-test-deploy enlightenment? We can help. Drop us a line at info@benday.com.